If you're in IT, or you need to be concerned about protecting your company's ability to do business 24/7, you have got to pay attention to what happened on October 21 when a distributed denial of service (DDoS) attack came knocking on Dyn's door (a domain name service provider).
You need to be vigilant and that is done by using the tools available in your network. You need to understand what happened last month and then put together a plan and course of action so that you don’t fall victim to a future attack that may have an even bigger impact on you and your business. Now is the time to make sure your networks and devices are safe from these types of attacks.
What is a DDoS?
A distributed denial of service attack can happen in several different ways. In this case, there was a deluge of web traffic that overwhelmed servers such that network service was denied to legitimate network users.
According to Dyn, the domain name service provider hit with the massive DDoS attack that day, there was a botnet – which is a computer network created by malware and controlled remotely without the knowledge of the users of those computers. This botnet consisted of an estimated 100k internet-connected devices, instead of the original estimates that there were tens of millions of IP addresses, that were responsible for the huge attack on critical systems.
For comparison, Gartner estimates there are currently 6.4 billion IoT devices, so relatively speaking, there was a very tiny number of devices involved – this time. These 100k devices were hijacked to flood Dyns’ systems with unwanted requests, shutting down the internet for millions.
What virus was involved in the attack?
The compromised devices were infected with the Mirai malware, an infamous virus that has the ability to take over cameras, DVRs, and routers. Mirai malware searches for IoT devices that are using their factory set passwords then uses them as part of a botnet to launch DDoS attacks.
Are there other viruses that could cause a DDoS?
Absolutely!
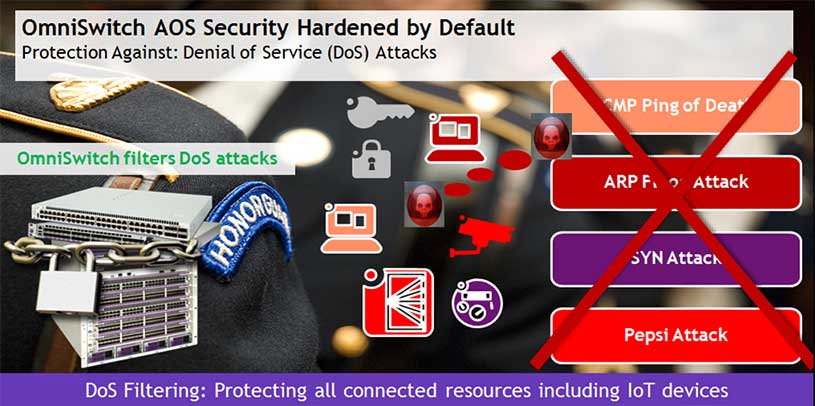
Although there are some attacks that take advantage of system bugs or vulnerability (such as teardrop attacks), most of these other types of attacks involve generating large volumes of traffic so that network service is denied to legitimate network users, such as this attack. These types of attacks include:
• ARP Flood Attack – Floods a network switch with a large number of ARP requests, resulting in the switch using a large amount of the CPU time to respond to these requests. If the number of ARP requests exceeds the preset value of 500 per second, an attack is detected.
• Land attack – Spoofed packets are sent with the SYN flag set to a host on any open port that is listening. The machine can crash or reboot in an attempt to respond
• ICMP Ping of Death – This is where ping packets that exceed the largest IP datagram size (65535 bytes) are sent to a host and crash the system
• SYN attack – This attack floods the system with series of TCP SYN packets, resulting in the host issuing SYNACK responses. The half open TCP Connections can exhaust TCIP resources, such that no other TCP connections are accepted.
• Pepsi Attack – The most common form of UDP flooding directed at harming networks. A pepsi attack is an attack consisting of a large number of spoofed UDP packets aimed at diagnostic ports on network devices. A pepsi attack can cause network devices to use up a large amount of CPU time responding to these packets.
There are more showing up every day including Invalid IP attack and Multicast IP and MAC address mismatch.
What can you do to protect your network?
Your network switches and IoT devices can be protected against DDoS by filtering. Your network switches can be set to detect various types of port scans by monitoring for TCP or UDP packets sent to open or closed ports.
• Packet penalty values set. TCP and UDP packets destined for open or closed ports are assigned a penalty value. Each time a packet of this type is received, its assigned penalty value is added to a running total. This total is cumulative and includes all TCP and UDP packets destined for open or closed ports.
• Port scan penalty value threshold. The switch is given a port scan penalty value threshold. This number is the maximum value the running penalty total can achieve before triggering an SNMP trap.
• Decay value. A decay value is set. The running penalty total is divided by the decay value every minute.
• Trap generation. If the total penalty value exceeds the set port scan penalty value threshold, a trap is generated to alert the administrator that a port scan can be in progress.
For example, imagine that a switch is set so that TCP and UDP packets destined for closed ports are given a penalty of 10, TCP packets destined for open ports are given a penalty of 5, and UDP packets destined for open ports are given a penalty of 20.
Of course, the smartest switches in the world won’t help you if you don’t monitor the notifications triggered by these events. That’s where a good network management system is crucial. A good resource is your local ALE representative.
What about your smart "things"?
Besides taking care of the network, things that you can do to protect your smart devices, at work and at home are:
1. Password – This is the easiest one to fix and most overlooked – change the factory default passwords that come with your device. In this DDoS case, the virus searched for default settings.
2. Update your software – As annoying as those reminders are to update your software, they often contain critical security updates. Take the time and update!
3. Prevent remote management – Disable the remote management protocol, such as, telnet or http that provides control from another location. The recommended remote management secure protocols are via SSH or https.
The next time DDoS comes knocking at your door, be sure your network is set up to notify you of these activities and know how to manage them. In a perfect world, your switch/router networking devices would have their filtering capabilities enabled by factory default. If you have further questions on how to make your network more secure using Alcatel-Lucent Enterprise solutions, or are interested in a deeper dive into the technology, please contact your nearest ALE representative.
Latest Blogs

Is Wi-Fi 7 worth it? Migration tips to avoid costly downtime
Before upgrading to Wi-Fi 7, organizations must ask: is Wi-Fi 7 worth it without upgrading their wired infrastructure first?

In AI, the First Mover Doesn’t Always Win
Why purpose-built solutions are overtaking incumbents, from chatbots to CRMs to network operations

Resilient by Design: Navigating the Future of 112 with Secu…
AI-powered public safety solutions enable secure, sovereign NG112 communications with resilient, standards-based integration.

Empowering businesses through choice: Why your cloud operat…
A flexible cloud operating model gives businesses the freedom to choose, communicate better, serve smarter, defend stronger, and grow bigger.





